It Takes Three Things for a Network to Withstand Cyber Attack
Cyber security requires a systemic approach to address three main tenets: availability, confidentiality and integrity. That’s because responsibility for the security of each is divided among the elements of a network, according to Vinit Duggal, Intelsat’s Director and Chief Information Security Officer, in an interview with Via Satellite.
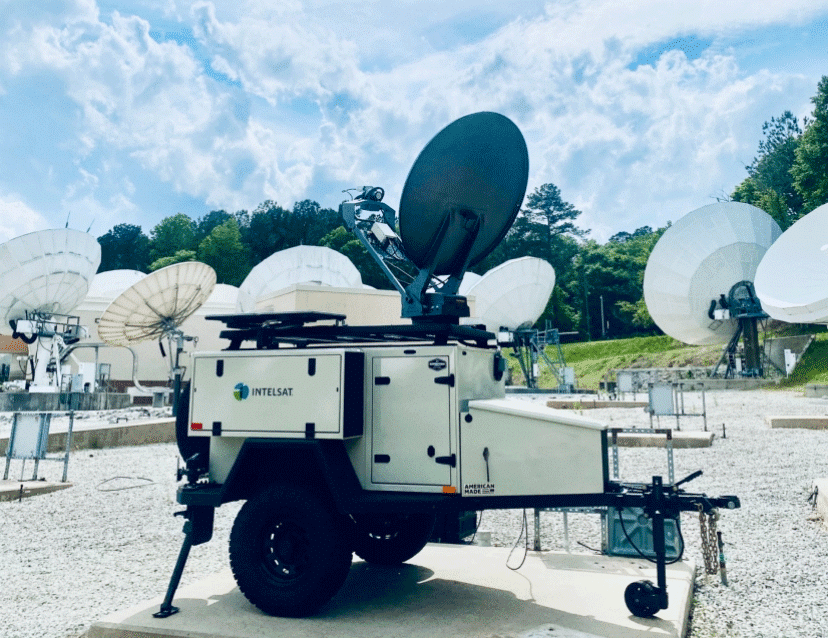
“The satellite operator is responsible for ensuring the availability of services – or making sure the path between the end users and teleport is always available,” Duggal said.
“… Confidentiality – or how the data passing through the network is stored and in what form it is transmitted and managed – is the responsibility of our customer, usually the service provider. The third piece, integrity of the data passing through the network, is a joint effort between the network provider and the end user. This can involve tasks such as encrypting data moving along the network, as well as educating network users to their individual responsibilities when accessing a network via a personal device.”
Intelsat is doing its part for to maintain the cyber security of available services with technology advances, such as the high-throughput Intelsat EpicNG family of satellites, the first of which was launched January 27.
“The architecture of … (the) Intelsat EpicNG platform, combined with our focus on satellite network security, provides a strong basis for hardening a network,” Duggal said. “The capabilities of our digital payload, the most advanced in the commercial sector today, provides improved jamming and interference protection by helping to identify potential issues and being able to rapidly shift customers out of the impacted spot beams into beams in which there is no sign of trouble.”
In the interview, Duggal also spoke of the potential value of Intelsat EpicNG to accommodate the expanding bandwidth needs of remotely piloted aircraft (RPAs), adding that security is paramount for Intelsat services to government and military, just as it is with commercial customers.
“[Intelsat EpicNG] spot beams and wider bandwidth segments support a greater range of protected waveforms, including those being developed by the U.S. military,” he said.
Intelsat General’s goal of meeting, or exceeding, DoD-mandated security requirements for information assurance is being met by assessing and building infrastructure, networks and third party infrastructures against the most stringent DoDI 8500.2 MAC Level I controls.
By Intelsat’s taking a systematic defense-in-depth approach that detects, prevents and mitigates attacks, information assurance is greatly enhanced. A comprehensive IA assessment and remediation program adds to that security. The program includes annual penetration assessments, organization wide control assessments and third party SOC3 audits of both satellite and terrestrial environments.
It’s a system of systems approach to security, one that lends itself to all of the security tenets.
For example, RPA security technology developers are also creating systems to support confidentiality and integrity, other tenets of cyber security, as enumerated by Duggal.
A recent SIGNAL Magazine article, “Cybersecurity for Unmanned Aerial Vehicle Missions,” gives examples of some efforts to cope with threats, including a University of Virginia-developed layer called System-Aware. By knowing the elements of the RPA systems being monitored, System-Aware platforms can address anomalies that could be indicative of a cyber attack.
One such cyber security monitor, called Sentinel, collects information of illogical behavior that could be evidence of a cyber attack. For example, Sentinel would notice a deviation of an RPA navigation system pattern not sent by the pilot. It would also spot a change in a camera’s aim not directed by the RPA’s sensor operator.
The threat can come from signals sent into the control stream or even a Trojan horse embedded in software. Perception of an anomaly can alert RPA controllers, who could be equipped with a switch to disable the camera, override the flight control system, or even thwart the cyber attack.
Sentinel is just one example of a System-Aware platform that shows developers are aware of their responsibility to address network elements of confidentiality and integrity, just as Intelsat is addressing availability.
It’s part of a growing awareness that all three are necessary parts of a space secure network, one that can best cope with ever-emerging cyber threats.